
Distributed denial of service (DDoS) attacks have become a routine occurrence in today’s digital realm. Organizations of all sizes, whether nonprofit entities or global corporations, can fall victim to these attacks that disrupt their online services—ranging from websites to email—by flooding their internet-facing resources.
This threat not only affects the integrity of network and service provision for tenants and subscribers of data centers, hosting providers, and colocation services but also poses a risk to high-value customers. The repercussions of a successful DDoS attack can tarnish brand reputation and incur substantial financial losses, ranging from hundreds of thousands to even millions of dollars.
Additionally, these attacks are often employed as a diversion tactic to deflect attention from concurrent criminal activities such as data breaches or network infiltrations.
A10’s threat research team has meticulously tracked DDoS weapons, revealing the identification of around 15.4 million weapons in 2021 – the A10 Attack Mitigation Threat Report (2H2021).
DDoS Attacks are more frequent & bigger than ever
The landscape of online threats is evolving rapidly, with hackers initiating an increasing number of DDoS attacks, targeting new objectives, and assembling larger botnets. The expansion of Internet of Things (IoT) devices due to the growth of 5G technologies and the demand for diverse business solutions have contributed to the creation of an extensive pool of vulnerable devices susceptible to being recruited for botnet armies.
Consequently, DDoS attacks are projected to intensify in both frequency and complexity, given the proliferation of botnets and affordable DDoS-as-a-service platforms.
The pandemic years have been particularly active for cybercriminals, marked by surges in DDoS weaponry, widespread botnet operations, and record-breaking attack magnitudes. The COVID-19 lockdown in 2020 drove a swift transition to online modes for various activities, from education to shopping, expanding the scope of potential targets for hackers. This abrupt shift left many businesses and individuals inadequately protected against attacks due to the challenges of maintaining robust cybersecurity measures during emergencies.
The Year of Record-Breaking Attacks
The year 2021 witnessed a significant escalation in the scale of DDoS attacks. Notably, Microsoft countered a DDoS attack in November, registering a throughput of 3.45 terabits per second and a packet rate of 340 million packets per second—reportedly the largest DDoS attack on record. This year also saw the emergence of ransom-based DDoS attacks, wherein attackers demanded payments to cease or prevent attacks.
Ongoing monitoring by A10 Networks has uncovered a consistent rise in the frequency, intensity, and complexity of DDoS threats, as detailed in the A10 Attack Mitigation Threat Intelligence Report (2H2021). Encouragingly, proven DDoS protection methods have proven effective even as the threat landscape becomes more challenging.
A Glimpse into DDoS History
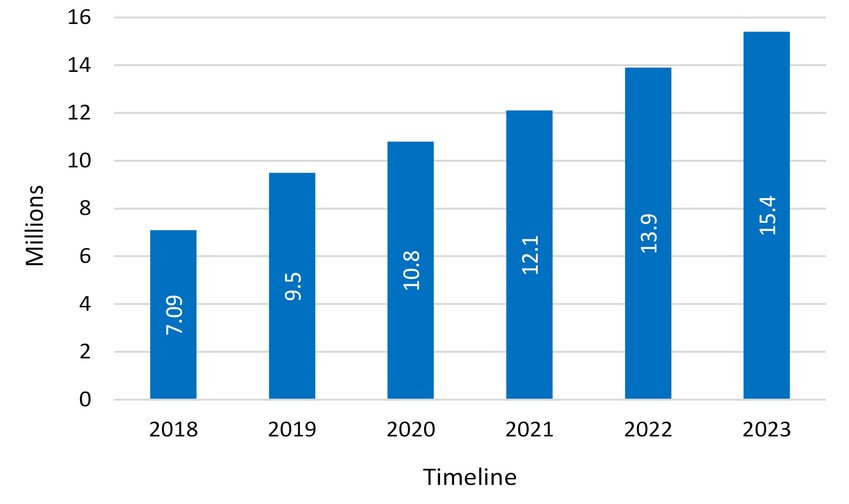
The first documented DDoS attack occurred in 1996 when Panix, a pioneer in internet service provision, suffered an extended outage due to a SYN flood—a tactic that has become synonymous with DDoS attacks. Over the years, DDoS attacks have become more common, with predictions indicating that the total number of attacks could double from 7.9 million in 2018 to over 15 million by 2023, according to Cisco.
The escalating scale of DDoS attacks is evident in the growth of botnets—networks of compromised devices used to generate DDoS traffic. As botnets expand, DDoS attacks become more formidable. Attacks of just one gigabit per second can incapacitate most organizations, but current peak attacks now exceed one terabit per second, driven by hundreds of thousands or even millions of compromised devices.
The Economic Toll of DDoS Attacks
Given the financial consequences of IT services downtime, which can amount to millions of dollars per hour, the impact of even a short DDoS attack is significant. To assess the potential effect of a DDoS attack on an organization and to enhance cybersecurity planning, refer to our white paper “How to Analyze the Business Impact of DDoS Attacks.”
The Most Notorious DDoS Attacks in History
To offer insights into the nature of these attacks, we delve into notable DDoS incidents that have shaped the threat landscape. Our selection includes attacks known for their sheer scale as well as those that have garnered attention due to their far-reaching impacts.
- The Google Attack in 2020: A Chinese-sourced UDP amplification attack targeted Google with a peak throughput of 2.5 terabits per second.
- The AWS DDoS Attack in 2020: Amazon Web Services faced a massive DDoS attack that exploited the Connectionless Lightweight Directory Access Protocol (CLDAP), reaching a peak of 2.3 terabytes per second.
- The Mirai Krebs and OVH Attacks in 2016: The Mirai botnet executed an attack on cybersecurity expert Brian Krebs’ site, followed by an assault on OVH with a traffic load of up to 1.1 terabits per second.
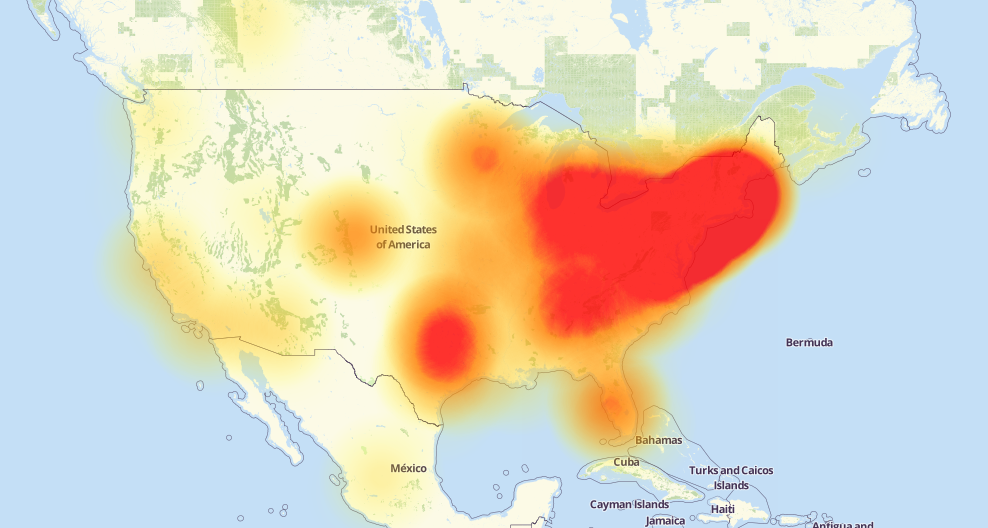
- The Mirai Dyn Attack in 2016: Dyn faced an attack generating up to 1.5 terabits per second, impacting high-profile websites like GitHub, HBO, and Twitter.
- The GitHub Attack in 2018: GitHub experienced a 1.35 terabit per second DDoS attack, highlighting the challenge of mitigation against such scale.
- European Gambling Company Attack in 2021: Akamai dealt with volumetric DDoS attacks of significant magnitude, reaching up to 800 gigabits per second.
- Occupy Central Attack in 2014: Hong Kong’s Occupy Central movement was targeted with attacks that peaked at 500 gigabits per second.
- CloudFlare Attack in 2014: CloudFlare faced an attack of 400 gigabits per second, demonstrating the exploitation of Network Time Protocol (NTP) vulnerabilities.
- Spamhaus Attack in 2013: Spamhaus suffered from a reflection attack of 300 gigabits per second, with attackers traced to a Dutch company.
- Six Banks Attack in 2012: Six major U.S. banks experienced DDoS attacks that generated over 60 gigabits per second of traffic each, allegedly attributed to the Izz ad-Din al-Qassam Brigades.
These instances underscore the diversity of attack vectors, the amplification techniques employed, and the profound impact on organizations’ revenue, reputation, and cybersecurity efforts. As DDoS attacks continue to evolve, proactive measures and resilient defenses remain crucial for safeguarding digital landscapes.
Protect your network against DDos Attacks: https://www.layerstack.com/en/ddos-protection


